Cybersecurity Services
ProArch delivers always-on threat detection and expert guidance to strengthen your defenses across IT, OT, AI, and data environments.
Actionable threat insights from ProArch’s SOC team
How Attackers Abuse Microsoft 365 Direct Send to Deliver Phishing Emails
Read MoreComprehensive Cybersecurity Services
We help you take control of your environment, your risks, and your rules, security built around how you operate
Security Advisory & Strategy
Define the right security roadmap.
- Virtual CISO (vCISO)
- Security Consulting
- Policies and Procedures
Assessments
Identify risks and benchmark your security posture.
- Penetration Testing
- Microsoft 365 Security Review
- Microsoft Zero Trust Assessment
- Security Assessment
- Security Posture Check
Security Managed Services
Continuous protection and support.
Less Risk. More Resilience. Real Results.
Microsoft Security Experts
Our Microsoft security experts maximize your protection and ROI.
In-House SOC
No outsourcing. Our SOC monitors, hunts, and responds 24/7.
Full Coverage. One Partner.
We protect everything your business depends on—IT, OT, Cloud, AI, data.
Specialized Cybersecurity Solutions
Your challenges don’t stop at IT. Neither do our cybersecurity capabilities.
Data Security
Ensure long-term trust with your clients by maintaining stringent standards for data security.
Data Governance
Know what data you have, where it lives, who’s using it, and if it meets compliance.
Microsoft Security
We deploy, configure, and manage Microsoft Security tools to effectively protect your critical assets.
Governance, Risk & Compliance
We integrate security with compliance mandates for holistic protection.
Meet Our Cybersecurity Experts
Your Trusted Microsoft Security Partner
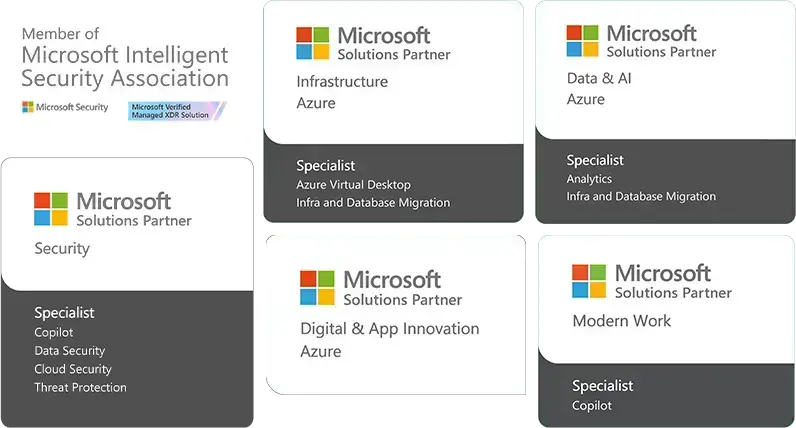
As a Microsoft Intelligent Security Association (MISA) member with multiple Security specializations, ProArch helps you maximize your Microsoft investment and stay ahead of evolving threats.
Cybersecurity FAQs
Do you provide 24/7 monitoring and response?
Yes. ProArch provides continuous 24/7 security monitoring and response through its our in‑house Security Operations Center (SOC). Threats are investigated, validated, and acted on in real time to reduce dwell time, contain incidents quickly, and minimize business impact without relying on outsourced or after‑hours escalation models.
What cybersecurity services are most critical for protecting Microsoft 365 environments?
The most critical cybersecurity services for protecting Microsoft 365 are identity and access security, email and endpoint protection, data loss prevention, and continuous threat detection and response—integrated and managed together to reduce risk across the tenant.
Should I outsource cybersecurity or build an in-house team?
A managed security partner can replace or augment an inhouse security team by providing 24/7 monitoring, threat response, and Microsoft 365 security expertise. This approach is often more cost effective and enables broader coverage than most internal teams can sustain alone.
Do you support both IT and OT (operational technology) security?
Yes. We deliver unified IT and OT security under a single program, extending monitoring beyond corporate IT into industrial systems like SCADA and PLCs. Our IT/OT specialists apply security controls without disrupting operations, giving energy, utilities, and manufacturing organizations full visibility across business and operational environments. Learn more on OT managed services here.
What should I look for when evaluating a Microsoft cybersecurity partner?
A strong Microsoft cybersecurity partner should have an in‑house SOC, deep Microsoft security specializations, MISA membership (ProArch is a Microsoft Intelligent Security Association member), proven IT and OT experience, clear incident response ownership, and the ability to operationalize Microsoft tools. These factors directly impact detection accuracy, response speed, and accountability during incidents.
What is managed detection and response (MDR)?
MDR (Managed Detection and Response) is a cybersecurity service that combines 24/7 human-led threat monitoring with advanced detection tools to investigate and respond to threats across endpoints, identities, cloud, and networks going far beyond antivirus or firewall-only protection.
How much do managed cybersecurity services cost?
Costs vary based on organization size, risk exposure, and service scope. From our experience, most organizations invest a small percentage of their overall IT budget in cybersecurity. Pricing is driven by attack surface, coverage requirements, and operational complexity, so engagements are scoped based on real risk, not fixed packages.
What happens during a live security incident and who leads response decisions?
During an active incident, ProArch’s SOC leads threat investigation, containment, and technical response while maintaining constant communication with the client. Clear escalation paths and decision ownership are defined upfront. Clients retain control over business decisions, while ProArch drives security actions, remediation guidance, and post‑incident reporting.
How quickly can ProArch’s cybersecurity services be implemented?
ProArch follows a phased approach that starts with visibility and risk assessment, then activating monitoring and response capabilities, so organizations begin reducing risk quickly without disrupting operations or overwhelming internal teams. Implementation timelines depend on scope and coverage requirements.
Can ProArch help with compliance and audits?
Yes. ProArch supports compliance by mapping security controls to required frameworks, identifying gaps, and providing evidence through monitoring, documentation, and reporting. We help organizations prepare for audits, respond to assessor questions, and maintain ongoing compliance rather than treating it as a one‑time activity.
Can ProArch work alongside an existing internal security or IT team?
Yes. ProArch commonly operates alongside internal IT or security teams in a co‑managed model. While internal teams focus on business initiatives and infrastructure, ProArch provides continuous security operations, threat response, and expertise reducing alert fatigue and strengthening overall security posture.
Your Stronger Protection Starts Here

Attack Surface Reduction Managed Service: Get protection across the productivity tools you use every day.
Having foundational threat defenses in place is vital. In today’s threat landscape, the traditional approach to security is not enough. When you rely only on firewalls and anti-virus, your organization is at risk. Attack Surface Reduction prevents malicious activity across systems, internet use, Office apps, email, and identities – the most common breaches.

Managed Detection and Response (MDR): Have a 24x7 team on your side proactively stopping cyber threats.
A security breach can put the brakes on company growth hurting your reputation, employee confidence, and relationships with customers. Avoiding these negative impacts to your business means having eyes on your corporate resources around the clock. ProArch’s Managed Detection and Response clients have peace of mind knowing an experienced security team is in their corner investigating and responding to cyber threats— 24x7.




